Digital identification is the focus of two reports by the European Union Agency for Cybersecurity (ENISA): an analysis of self-sovereign identity (SSI) and a study of major face presentation attacks.
Trust in the identity of a natural or legal person has become the cornerstone of our online activities. It is therefore essential that digital identity is kept highly secure for a safe access to financial services, e-commerce, delivery or transport platforms, telecommunications and public administration services.
EU Agency for Cybersecurity, Executive Director, Juhan Lepassaar stated that “With the unrelenting circulation of the COVID-19 virus and the continually growing need to rely on digital services, securing electronic identification remains a critical target to achieve the resilience and trust of the digital single market.”
Under this light, it is the purpose of the EU regulation on electronic identification and trust services, or eIDAS Regulation, to provide a common foundation to secure electronic transactions between citizens, businesses and public authorities.
A key objective of the eIDAS regulation is to secure electronic identification and authentication in cross-borders online services offered within Member States. Today’s publications support the achievement of this objective of the regulation. In addition, the regulation also addresses identity proofing in the different contexts where trust in digital identities is necessary and elaborates on qualified certificates to allow for other identification methods.
The area of identification has seen a new trend emerge over the past few years in the self-sovereign identity technologies also referred to as SSI. The report explains what these technologies are and explores their potential to achieve greater control of users over their identities and data, cross-border interoperability, mutual recognition and technology neutrality as required by the eIDAS regulation.
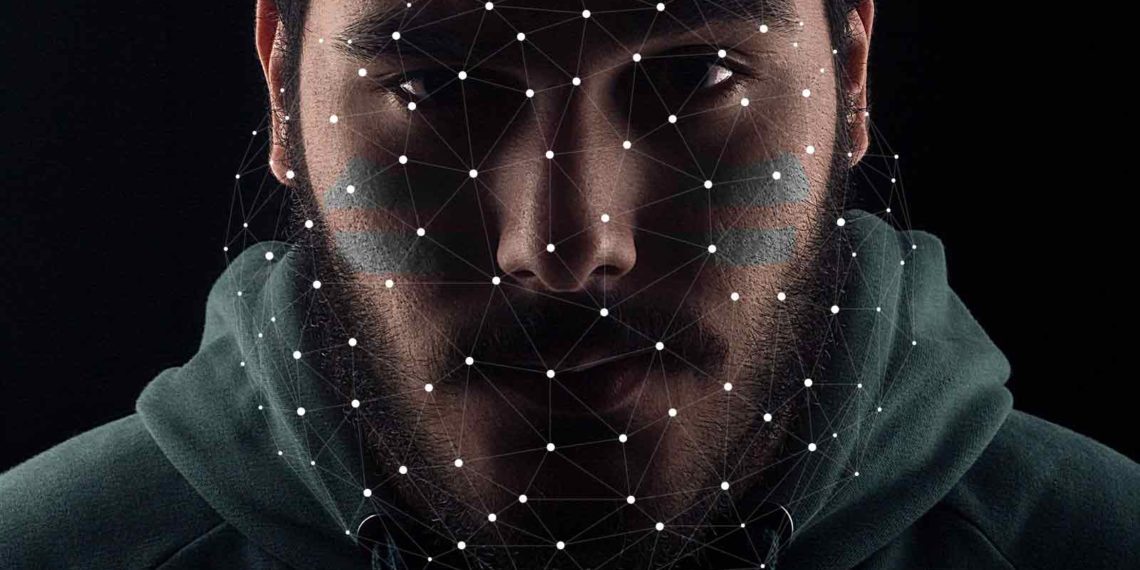
The report on remote identity proofing builds on the previous report Remote ID Proofing of ENISA, which makes an analysis of the different methods used to carry out identity proofing remotely. The new report analyses the different types of face recognition attacks and suggests countermeasures. It also validates the security controls introduced in the previous report and offers further recommendations on how to mitigate identified threats.
Face presentation attacks in remote identity proofing methods
What do we need to know?
Remote identify proofing process is usually carried out over a webcam or a mobile device. The user shows his or her face to produce official documents such as legal identity cards or passports.
However, criminals have devised a number of tactics to bypass the security of these systems and impersonate someone else.
The analysis presented in the report published today identifies the different remote identity proofing methods and explains the different features of the major face presentation attacks as listed below:
- photo attacks based on the presentation of facial evidence of an image of a face printed or displayed via a device’s screen.
- video of user replay attack usually consisting of placing the screen of the attacker’s device in front of the camera.
- 3D mask attacks where 3D masks are crafted to reproduce the real traits of a human face and even include eyes holes to fool the liveliness detection based on eye gaze, blinking and motion.
- deepfake attacks make use of leveraging software capable to create a synthetic video or image realistically representing someone else. Attackers are suspected to have access to a wide dataset containing images or a video of their target.
What can be done to prevent them?
The study includes recommendations and identifies the different types of security controls, which include:
- environmental controls, such as setting a minimum video quality level
- identity document controls, such as checking that a document is not lost, stolen or expired in relevant databases
- presentation attack detection, such as checking user’s face depth to verify it is three-dimensional or looking for image inconsistencies resulting from deepfake manipulation
- organisational controls, such as following industry standards.
There is no ideal choice when it comes to the choice of the countermeasures to implement. The best choice(s) remains the one(s) pertaining to the type of business, the profile and number of users and the degree of assurance you wish to achieve.
What is self-sovereign identity (SSI)?
The technologies falling under the name of self-sovereign identity (SSI) consist in giving identity holders greater control over their identity. The main advantage of the SSI technology is that it gives the user greater control over how its identity is represented to third parties relying on the identity information. More specifically it gives greater control over the personal information. Users can have multiple “decentralised identifiers” issued for different activities and can separate out the attributes associated with each identifier.
Those decentralised digital identities can be used to support pseudonyms for privacy of identity. The separation of potentially private attributes from the digital identity is therefore enabled and the user can select the attributes to be disclose to ensure the privacy of the other attributes.
Recommendations
A number of elements need to be considered in relation to governance of the architecture of an SSI solution such as the certification of wallets for instance.
Key security measures in relation to risks presented by the SSI architecture need to be implemented, such as:
- data minimisation – using only necessary data
- consent and choice – in which the user controls the process and data used for identification
- accuracy and quality – where all parties can trust the identification data stored and provided by the wallet.
EU’s Digital Identity proposal
The EU Agency for Cybersecurity welcomes the European Commission’s proposals that will review the eIDAS regulation. The European Digital Identity is intended to be available to all EU citizens, residents and businesses in order to identify themselves or provide confirmation of personal information. Citizens will be able to prove their identity and share electronic documents from their European Digital Identity wallets with the click of an icon on their phone. They will be able to access online services with their national digital identification, which will be recognised throughout Europe.
The new European Digital Identity Wallets will allow all Europeans to access online services without having to resort to private identification methods or share unnecessary personal data. Thanks to this solution, users will have full control of the data they share.
Credit: Source link