High-risk, widespread vulnerabilities cause significant disruptions to already struggling security teams. In 2021, 1100+ CVEs with 9-10 CVSSv3 scores flooded the tech ecosystem. Fixing a critical vulnerability takes 100+ days on average and some may take years to eliminate through patching or other solutions.
So how can security specialists cope?
Automation is an option, as teams still do a lot of manual work to confirm the real impact of a CVE with remote code execution risk. Without dependable help, penetration testing and vulnerability assessments can burden security pros until they burn out, which is already a widespread problem.
Because we care about this problem, our research team at Pentest-Tools.com built a tool to help security teams confirm which of their systems are truly vulnerable – a lot faster and more reliably.
Using real attack methods to validate scan results – without disrupting the target
A seasoned offensive security pro knows where automation makes a real difference and where it’s impractical or risky. Pentesters take calculated risks all the time. They balance curiosity with control to comb for high-risk vulnerabilities that can actually trigger damaging consequences. But it takes time and painstaking effort, which they can’t always afford.
We developed Sniper – Automatic Exploiter to simulate real exploits and attack techniques threat actors use – and do it significantly faster. Sniper bridges the gap between results that common vulnerability scanners produce and adversarial tactics cybercriminals employ to gain system access.
When a CVE like Log4Shell (CVE-2021-44228) surfaces, Sniper automatically finds systems vulnerable to its targeted intrusion techniques. By automating how you validate widespread CVEs with Sniper, you minimize the window of opportunity for attackers. This helps avoid aggressive exploitation campaigns that always follow high-risk vulnerability disclosures.
What Sniper Automatic Exploiter does (and how it does it)
This custom tool uses a set of modules to mimic real-world exploits and attack techniques and determine vulnerable systems – in a fraction of the time compared to manual exploitation.
Here’s how Sniper Auto-Exploiter works:
1. Scans for open ports
Checks if the TCP ports specified as input are open or not. This lists open ports, along with the protocol, type of service, and its version.
2. Fingerprints web services
It iterates through each port that runs a HTTP/S service and tries to determine what type of web application is running and which technology sits behind it.
3. Looks for compatible exploits
Based on the fingerprint data it automatically collected, Sniper filters through a list of exploits to find the right match (list excerpt below).
4. Checks if the target is vulnerable
Runs the check routine for each compatible exploit to determine whether the target is exploitable – without extracting any data.
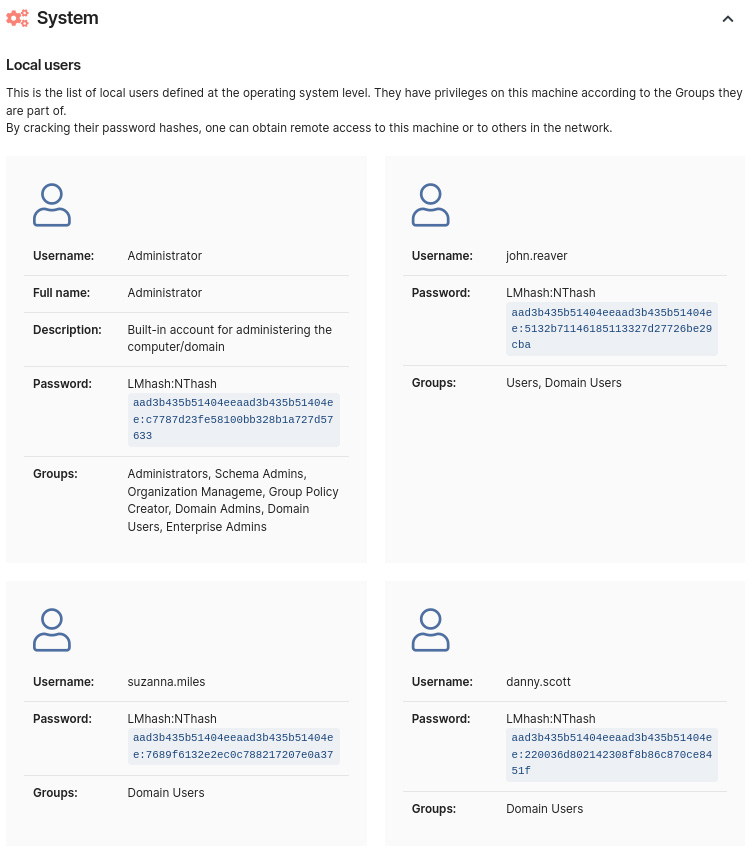
5. Exploits and extracts all artefacts
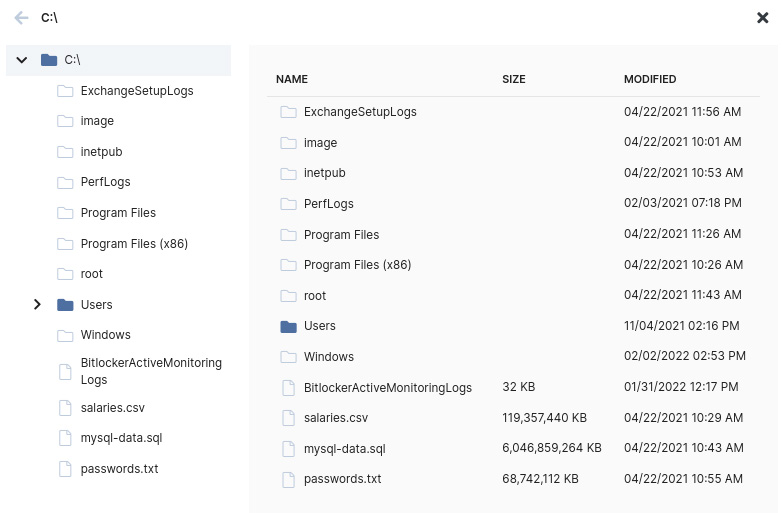
If the target is exploitable, Sniper automatically extracts all the artefacts, capturing them in the output report.
6. Cleans up
Most exploit modules don’t create any files or processes on the target system, so no cleanup is necessary. However, when they do, Sniper deletes them and leaves the system unaltered and clean.
Sniper helps you gain RCE on vulnerable targets in minutes and gets you solid proof for vulnerability validation. With this reliable evidence of compromise, you can report your findings and prioritize systems for effective remediation.
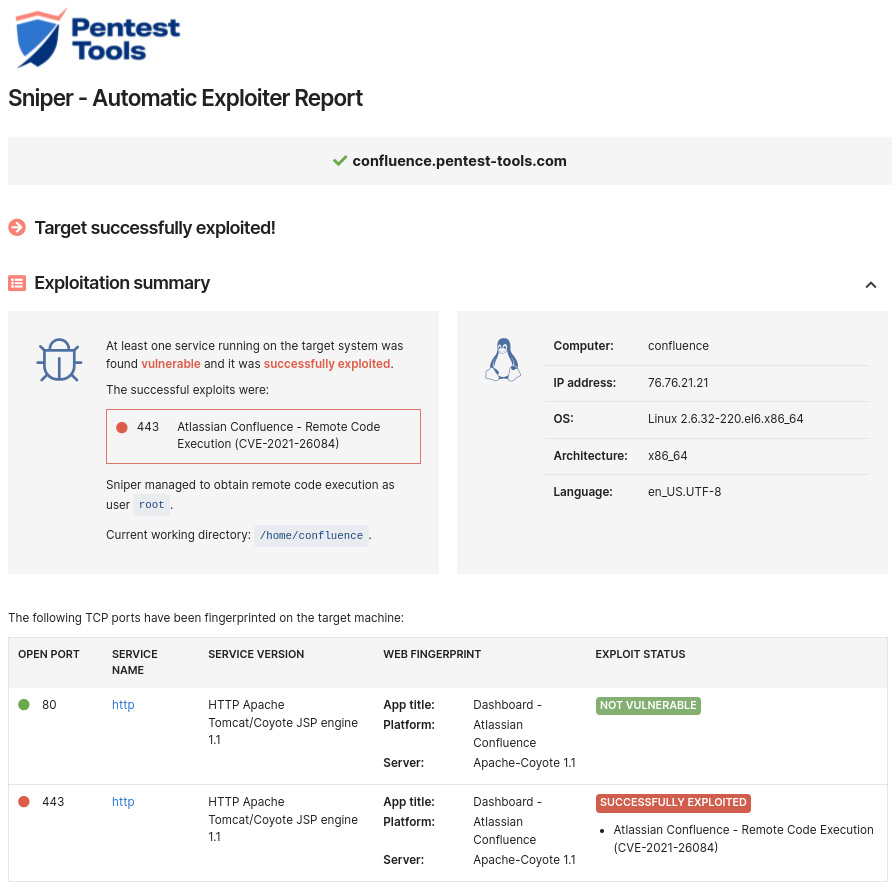
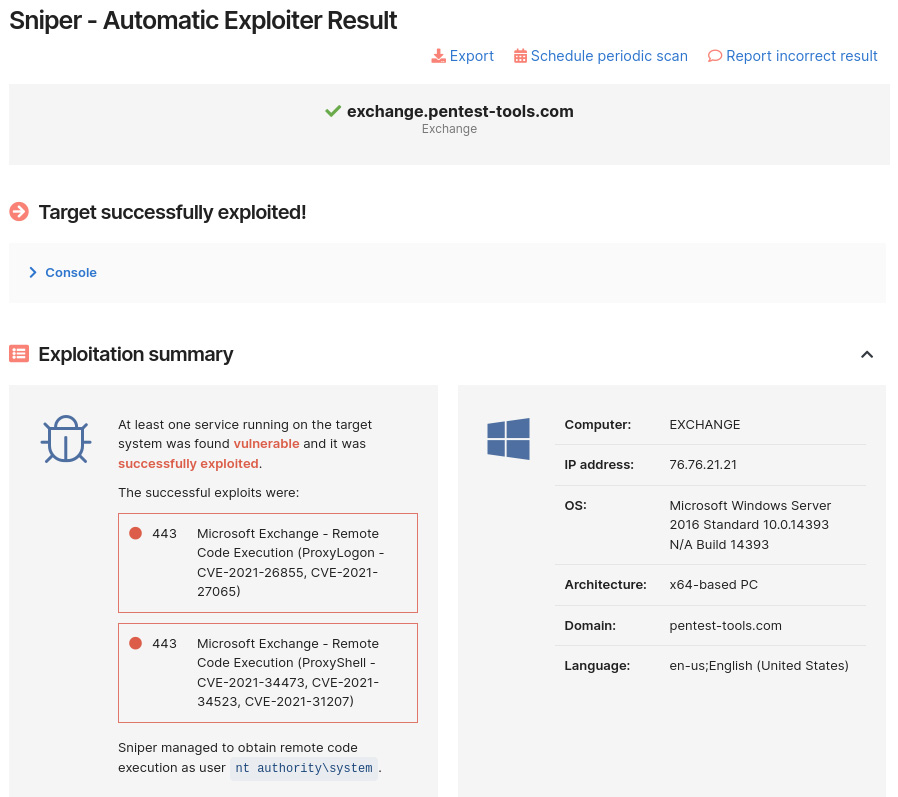
Here’s a snapshot of the Sniper Automatic Exploiter report:
3 ways to use Sniper Automatic Exploiter
Sniper is an excellent companion for penetration testing engagements and other offensive security activities.
Gain initial access:
- gain initial foothold with zero effort
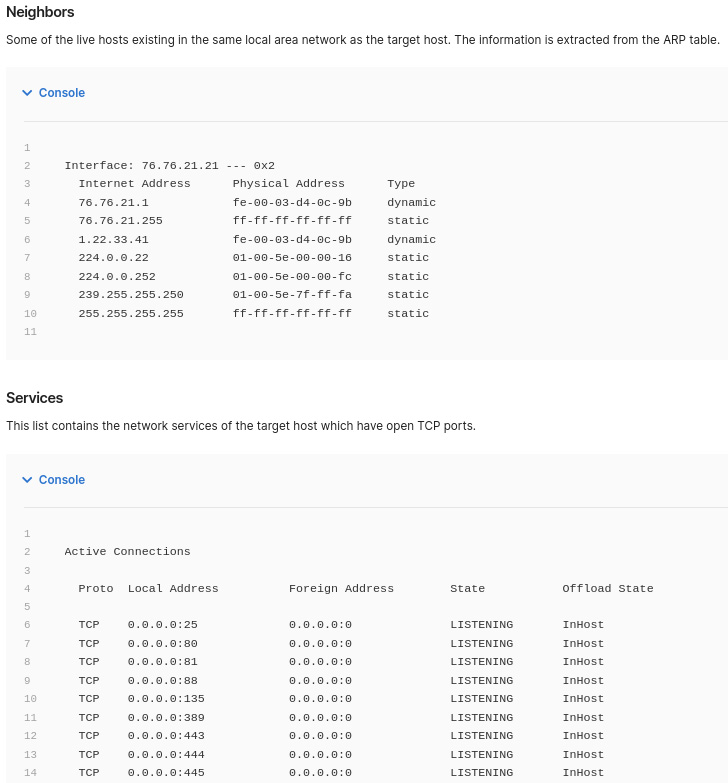
- automatically gather information for lateral movement and recon
- speed up exploitation for vulnerabilities that require urgent remediation.
Sniper reduces your workload by hours when you need to simulate realistic attacks and gain access to the machines in the target network. Plus, you can use it from anywhere, since it’s part of the cloud-based Pentest-Tools.com platform.
Vulnerability validation:
- confirm if vulnerabilities that scanners report are exploitable
- quickly filter out noise vulnerability scanners create
- eliminate false positives.
When Sniper successfully exploits a CVE, it confirms the risk is real. It also means attackers are actively exploiting it, making remediation urgent.
Controlled exploitation:
- run full automatic exploitation and save time
- eliminate the risk of human error
- leave the target system unaltered and clean.
Sniper doesn’t give unrestricted shell access to the target system. Instead, it does full automatic exploitation by itself. This safer approach eliminates potential human errors during the attack phase. It also ensures exploitation leaves the target in a good and clean state.
Automatically exploit new, high-risk CVEs with Sniper
As with all the tools on our platform, we keep Sniper – Automatic Exploiter up to date, integrating new, widespread vulnerabilities as fast as 72 hours (on average) after they get a CVE.
No one can exploit a vulnerability like you do. But, with the right tools, you can scale your expertise to cover more critical vulnerabilities, faster. Our goal is to help you accomplish this.
Credit: Source link